STeBB
STeBB ( Security Testing Browser Bundle ) is an all in one web security toolkit for web application security testers. Built over Mozilla Firefox, this Linux based open source browser bundle comes with a vast array of awesome tools that help you secure your web application. STeBB runs in Debian based Linux distributions and can be used to thoroughly security test the web applications, especially the OWASP Top 10 risks. Basically it’s a web pen testing browser bundle.
Installation issues
I wanted to install STeBB in a Kali VM. Running the portable version resulted in a number of errors. A reply on a post on Google+ provided useful information to deal and solve these errors.
The first error was
No such file or directory
This error could be solved by installing the ia32-libs. STeBB is compiled against 32 bit and the Kali VM was 64 bit so the necessary libraries were missing.
dpkg --add-architecture i386 apt-get update apt-get -f install dpkg --configure -a apt-get install ia32-libs
After installing these libraries I got one step further but I still had this error
XPCOMGlueLoad error for file /root/STeBB/libxpcom.so: libdbus-glib-1.so.2: cannot open shared object file: No such file or directory Couldn't load XPCOM.
This was solved by installing the extra 32 bit gtk library.
apt-get install ia32-libs-gtk
STeBB add-ons
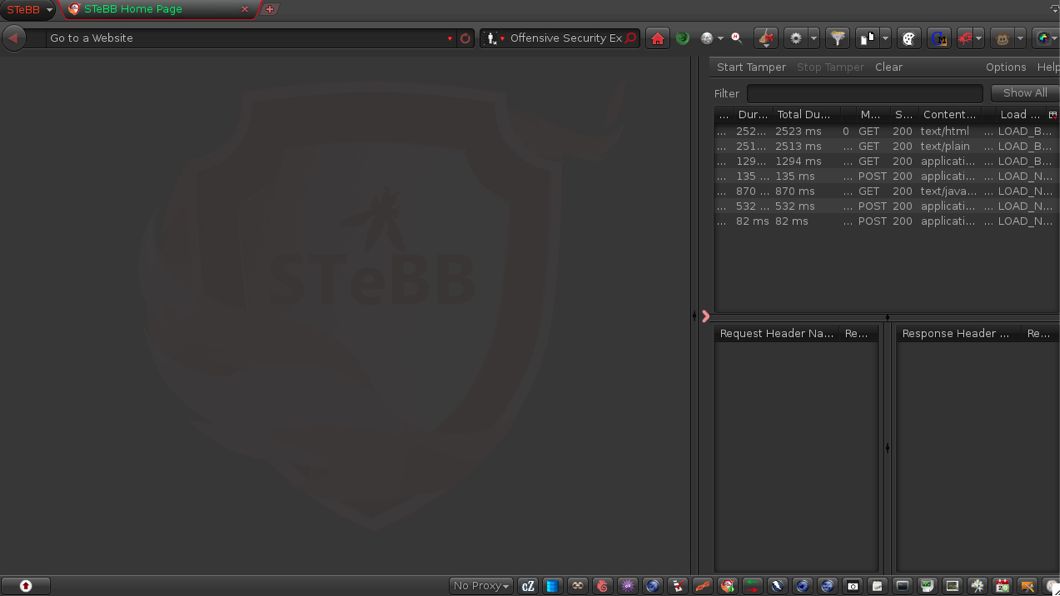
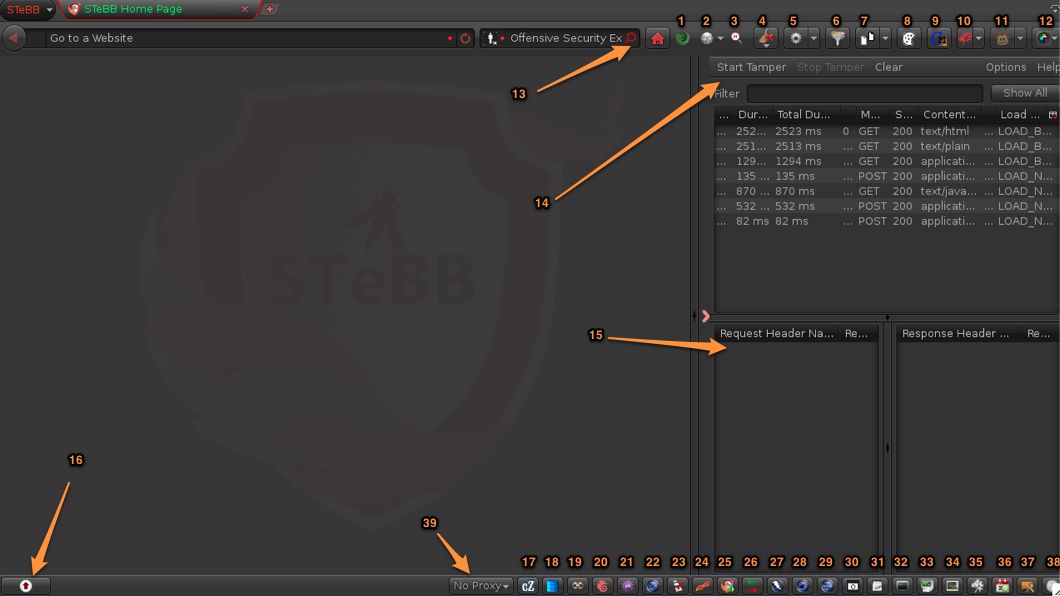
STeBB comes with an overwhelming set of extra add-ons and tools. Below is an overview.
The main navigation bar is similar to a default Firefox bar, with extras.
- Show or hide the hackbar;
- Switch user agent;
- HackSearch button, search in some of the ways hackers would to gather google indexed data about your website so that you can secure it yourself;
- Clear console, one click to clear your cache, cookies, history, html5/local storage, http logins, all of them or restart your browser with/without notifications;
- Web developer, the Web Developer extension adds various web developer tools to the browser;
- Email extractor, extracts all the emails in from the current browser tab and/or the entire browser tabs;
- Refcontrol, control what gets sent as the HTTP Referer on a per-site basis;
- Cookies manager, cookies manager to view, edit and create new cookies. It also shows extra information about cookies, allows edit multiple cookies at once and backup/restore them;
- Cookie Monster, Cookie Monster provides proactive cookie management on a site or domain level basis, including 3rd party cookies. Via the status bar, it provides easy access to enhanced cookie functionality, while doing so in a non-intrusive manner;
- Firebug, a web development tool;
- GreaseMonkey, customize the way a web page displays or behaves, by using small bits of JavaScript;
- Awesome Screenshot, Capture, Annotate and Share.
The search form gives access to a number of online search engines. There are also some new panels (right pane and bottom pane).
- Web search (Shodan, RFC, …), similar to the default search form;
- Tamper data, main screen;
- Tamper data, request / response screen;
- STeBB extra panel (see below).
The status bar of the browser window gives you access to a very large set of add-ons and system tools.
- chatzilla, a clean, easy to use and highly extensible Internet Relay Chat (IRC) client;
- sqlite-manager, manage any SQLite database on your computer;
- Links;
- fireftp, a free, secure, cross-platform FTP/SFTP client for Mozilla Firefox which provides easy and intuitive access to FTP/SFTP servers;
- firessh, a free, cross-platform SSH terminal client for Mozilla Firefox. Written entirely in Javascript;
- About OWASP;
- The OWASP pentesting checklist;
- Pointer to a number of ‘hot links’;
- Vidalia TOR, client for the TOR network;
- HTTPrequester, a tool for easily making HTTP requests (GET/PUT/POST/DELETE), viewing the responses, and keeping a history of transactions;
- ZAP proxy, an easy to use integrated penetration testing tool for finding vulnerabilities in web applications;
- Webscarab, a framework for analysing applications that communicate using the HTTP and HTTPS protocols;
- Webslayer, a tool designed for brute forcing Web Applications, it can be used to discover not linked resources (directories, servlets, scripts, etc), brute force GET and POST parameters, brute force forms parameters (User/Password), fuzzing, etc.;
- Screenshot;
- Gedit;
- Start a terminal;
- System log;
- System monitor;
- Network tools;
- Task scheduler;
- System settings;
- Memory Monitor.
On the bottom left, there’s a button that opens an extra panel (#16). This panel provides access to a couple of extra scanner tools.
- Nikto web scanner, an Open Source (GPL) web server scanner which performs comprehensive tests against web servers for multiple items, including over 6500 potentially dangerous files/CGIs, checks for outdated versions of over 1250 servers, and version specific problems on over 270 servers;
- Wfuzz, a tool designed for bruteforcing Web Applications, it can be used for finding resources not linked (directories, servlets, scripts, etc), bruteforce GET and POST parameters for checking different kind of injections (SQL, XSS, LDAP,etc), bruteforce Forms parameters (User/Password), Fuzzing,etc.;
- A REST client, a debugger for RESTful web services;
- Notes;
- Cryptofox, an encryption/decryption tool for Mozilla Firefox, with dictionary attack support for cracking MD5 passwords;
- STeBB history;
- SQL Inject me, a Firefox Extension used to test for SQL Injection vulnerabilities;
- XSS me, a Firefox Extension used to test for Cross-Site Scripting vulnerabilities.;
- Create a report inside STeBB by -manually- adding the vulnerabiilty information.
No interoperability
The list of included tools is very impressive but I found it annoying that there does not seem to be a real ‘interoperability’ between the different tools.
I often use httprequester because it’s an easy to use tool to create custom HTTP requests. If you use the browser address bar to go to a site (maybe use the web developer add-on to isolate the AJAX request that you want to analyse) then the URL is not immediately put in the request field of httprequester. This is comparable to the features (or lack of) provided by getting Firefox and adding the add-on yourself. After all, STeBB is a bundle and not a separate security testing application.
PenQ history
STeBB was born as a fork of PenQ. This is something that you’ll notice when using some of the tools. For example, when I wanted to run nikto it raised an error because of a non existing directory.
/usr/share/STeBB/utilities/runNiktoTerminal: 69: /usr/share/STeBB/utilities/runNiktoTerminal: cannot create /home/kaliuser/.penq/nikto_results/niktoscan20131212_150624.txt: Directory nonexistent
You can get by this error by creating the necessary directories but it’s annoying never the less.
Conclusion
I think that STeBB is a very good starting place if you want to get introduced to a large set of (new?) tools that can be very useful for a penetration tester. However, once you know what these different tools do, how you should use them and you know what set of tools are fit for you then the STeBB bundle becomes to heavy on resource-usage compared to your own custom solution.