Introduction
Tor protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world: it prevents somebody watching your Internet connection from learning what sites you visit, and it prevents the sites you visit from learning your physical location (from https://www.torproject.org/).
There are Tor Bundles that you can install but you can also chain Tor through a proxy.
I’ll use an Ubuntu 1214 vmware machine to proxy my traffic. The VM has one shared network interface.
Privoxy
Privoxy is a non-caching web proxy. It has some filtering capabilities but for this setup I’ll only use the proxying capabilities.
Installing privoxy on Ubuntu is straightforward
apt-get install privoxy
The configuration of privoxy is done in /etc/privoxy/config. On a VM setup you can configure privoxy to listen on the public interface
listen-address 0.0.0.0:8118
To increase anonymity you should disable logging by commenting this line
# logfile logfile
Then set privoxy to chain the traffic to Tor
forward-socks5 / 127.0.0.1:9050 .
Tor
Now we’ll have to install Tor. There’s an Ubuntu package for Tor.
apt-get install tor
That’s all there is for getting Tor started.
By default, the Tor proxy is set to server type 4. If you want to use it chained with privoxy you have to switch to type 5.
server_type = 5
Setting the proxy in a browser
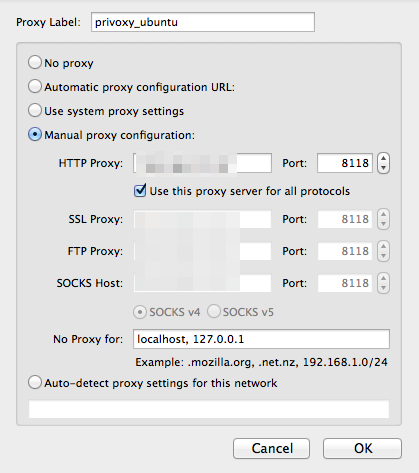
Most browsers can be configured to use a proxy. Changing the configuration can be a pain if you want to switch often between using the Tor proxy or not. Firefox has a plugin that can take care of this switching and it is called Proxy Selector.
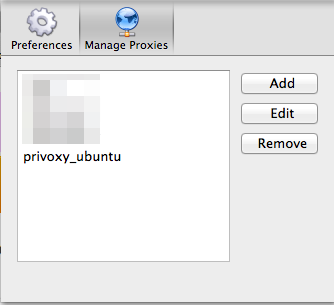
After installing the plugin you can add your new proxy. By default privoxy runs on tcp/8118.
Testing
Start both services.
/etc/init.d/tor restart /etc/init.d/privoxy restart
Make sure the proxy settings are correct and now point your browser to http://config.privoxy.org/show-status. Privoxy will intercept this request and show you its configuration settings.
Now you’ll have to check that your newly configured browser is using Tor. With the proxy disabled (or via another browser that is not using the proxy) go to the website http://whatismyipaddress.com/. Note the IP. Then enable the proxy and visit that website again. It should list another IP. Do the same for SSL enabled websites (https) via https://ipdb.at/.
Other applications
Tor can act as a SOCKS proxy for other applications. Open the configuration file /etc/torsocks.conf and search for the option server_type to set the SOCKS proxy type.
Legal issues
The legal framework and why (or why not) you should use Tor is described in detail on the Tor Exit Router information page of UCL.


I.m no expert but this seemed doable and usefull.I managed to install and activate privoxy but after installing tor things became difficult.I searched everywhere for this server switch line.
Activated the forwarding socks5 option also did not help.Tried to search for better info on the web and magazine but ended up deleting it all.
Just so that I can sleep at night.where do you switch the server from 4 to 5?