Traffic to C&Cs or interesting networks
Recently I had to verify traffic in a netflow collector for connections to a list of interesting networks (networks suspected to serve malicious content or C&Cs). The netflow collector that was used was an Arbor Peakflow solution.
Arbor Peakflow raw traffic
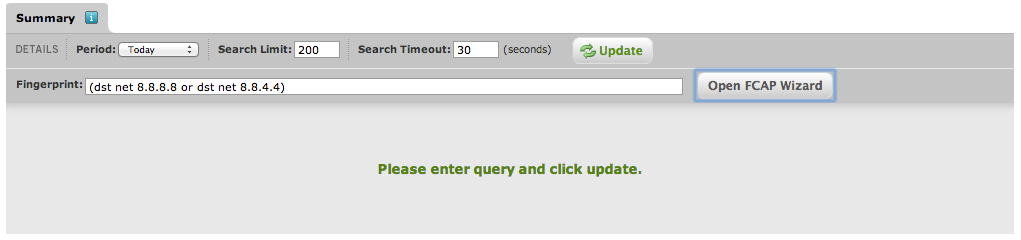
In Arbor you can browse the raw flows via Explore -> Forensics.
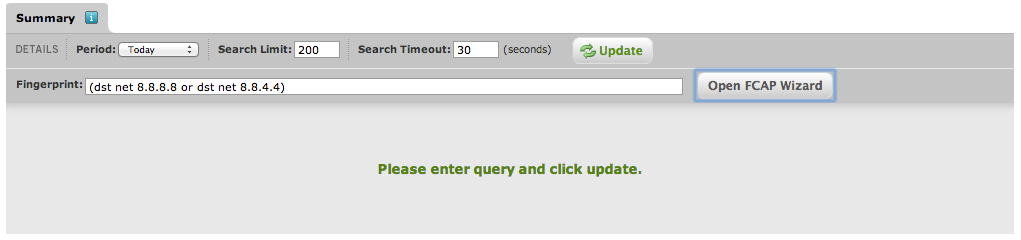
This feature allows you to look for specific traffic based on a FCAP filter.
Arbor Peakflow API
Before you can use the API, you need to generate an API key. In Arbor Peakflow, navigate to the menu Administration -> Arbor API Web Services.
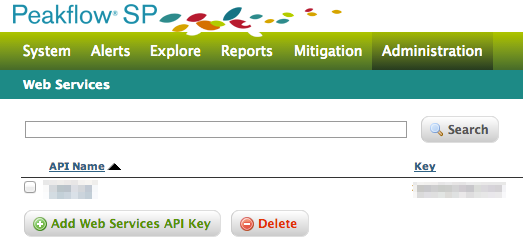
Then choose Add Web Services API Key. Add a descriptive name and click Save.
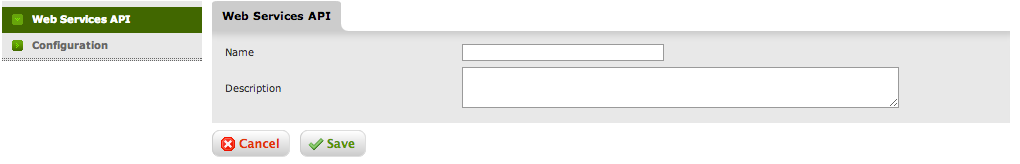
Once the entry is saved you’ll have to edit the entry and enable the key.
Python script to access Arbor Peakflow API
I wrote a small Python script that queries the Arbor API, parses the returned XML file and sends an email with the results.

The script is also hosted on Github. You can download the raw version at https://github.com/cudeso/tools/blob/master/get_rawdata_arbor.py.
The script is configured inline
- url : the URL containing the CSV file with the list of IPs and networks
- dst_ip_in_csv : the field that contains the IPs or network in the CSV file
- request_url : the URL to access the Arbor API (https://arbor.host.com/arborws/traffic?)
- api_key : api_key for Arbor Peakflow
- timeout : timeout for Arbor Peakflow request
- search_limit : limit results
- mail_rcpt : mail receiver
- mail_from : mail sender
- mail_server : mail server to use
The content of the mail is a CSV file containing
src_ip, src_port, dst_ip, dst_port, proto, packets, bytes x.x.x.x,37020,8.8.8.8,53,17,100,6200 x.x.x.x,45908,8.8.8.8,53,17,100,7000 x.x.x.x,57855,8.8.8.8,53,17,100,7000 x.x.x.x,2480,8.8.8.8,53,17,100,7200 x.x.x.x,45833,8.8.8.8,53,17,100,7000


Thank you, didnt find any API resources online, this script made it easy 🙂
Hi
I want to retrieve the mitigation information running in SP tool using requesting mitigation API and place it on NMS tool. Can you please help me in it.