Secure transfer of files, a central file transfer server for Windows
There are several solutions for copying files between Windows hosts, the protocol that most file transfers in the Windows world will default to is SMB (yes, thats the same protocol as used by Wannacry). What alternatives are available? The pre-requisites are
- Audit and logging capabilities, each transfer should be logged;
- One central server where files get pushed to and pulled from;
- Authentication, before a file transfer can happen, the user should authenticate;
- Secure transfer of files, meaning traffic that is not easy for attackers to eavesdrop. Although the transfers happen on an internal network precautions should be taken so that attackers can not eavesdrop on transfers (or alter these files in transit). In 2017 it would be very shortsighted to consider your internal network as “100% safe”.
- Only use tools that are available in a standard setup, no 3rd party software.
Secure FTP on Windows
For this blog post I decided to give secure FTP (note, this is not SFTP) a try. Secure FTP is available in Windows Server 2016 via the IIS component.
I started by downloading an evaluation version of Microsoft Windows 2016 server via https://www.microsoft.com/en-us/evalcenter/evaluate-windows-server-2016/ and install it as a VM.
Installing IIS
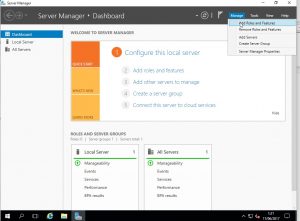
The first component I had to install was IIS. This is straightforward on a new install of Windows server. Use the Server Manager, select Manage and then Add Roles and Features
The wizard asks you to choose between role-based or RDP. Choose role-based and select the server you would like to configure. Then choose Web Server (IIS)
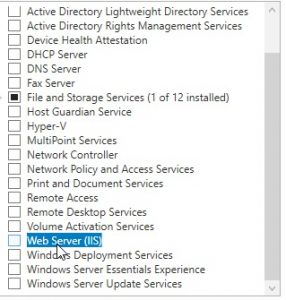
Add the feature and click a couple of times on “Next”.
We only want a secure FTP service, so there’s no need for the other IIS components. Disable the other components, select FTP and leave the management console for IIS enable.

Then choose Next and Install.
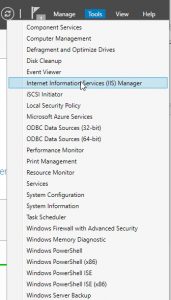
Now configure the IIS component via the Tools menu.
Configure secure FTP server on IIS
The first thing you now have to do is create a certificate. In the IIS administration console choose Server Certificates. You can then import a previously created certificate (preferred) or create a self-signed certificate.

For the purpose of this post I created a self-signed certificate but in a production environment you should import a valid certificate created by your certificate authority.
Configure secure FTP on IIS
Now it’s time to create a secure FTP host. Right click on sites and add FTP host. Select a name and a path where this FTP site points to.

Then choose the option to require SSL and choose the SSL certificate.

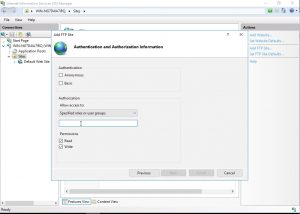
The next screen is about authentication. Ideally you should not allow everyone to access the file transfer service. You should create a dedicate Windows (either local or domain) group and then add the users that are allowed to access the server to this group.
For this blog post I also enabled “Basic Authentication” as authentication scheme, in a production environment you can choose your own authentication providers. Similarly, merely for this exercise I did not add other users and used the Administrator account for testing the setup.
That is basically all that is required to setup a secure FTP server on Windows.
Test the secure FTP server
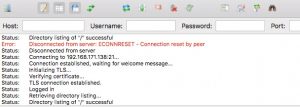
You can then use any FTP client that supports SSL. For example FileZilla
Recommendations
Although the above described process gives you a working setup there are some extra things to consider
- Use certificate based authentication;
- Enforce a retention policy for the files on the transfer server;
- Enable detailed auditing, logging and alerting of access attempts. Include both successful and failed access attempts.
- Include anti-malware solutions that scan the uploaded files, potentially blocking them if something unwanted has been found.
The goal of this exercise was to have a relatively secure file transfer service that’s easy to setup and use the tools build into Windows 2016. If you are allowed to install additional software then certainly have a look at SFTP or SCP, the file transfer server that runs over SSH.


All the steps need to be followed by windows users to secure windows file copy. And it is also necessary that Windows users need to install an antivirus tool to protect their data and personal information.