Drupal core update SA-CORE-2018-002
The Drupal team released a security advisory for all Drupal sites recommending all these sites to upgrade to the latest Drupal version.
The discovered vulnerability could lead to remote code execution in Drupal 7.x and 8.x.
Vulnerability
I have a mindmap on this vulnerability
Further information from Drupal can be found at
- Drupal core – Highly critical – Remote Code Execution – SA-CORE-2018-002
- The FAQ on SA-CORE-2018-002
According to bojanz this vulnerability is related to PHP’s improper sanitization in the handling of arrays in parameters (in GET/POST).
Impact
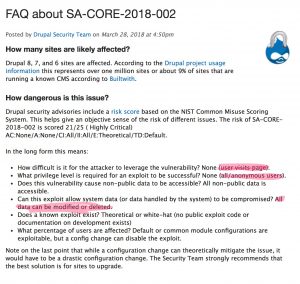
In essence the vulnerability describes a problem where
- an anonymous user visits a page
- exploits the vulnerability, allowing the attacker to
- view all non-public data
- modify or delete all the website data
This means that anyone on the internet can
- Steal all the information, including personal data, from your website
- Use your website to distribute malicious information
- Use your website to attack other organizations
Drupal does not use the CVSSv3 calculator but uses the NIST Common Misuse Scoring System (NISTIR 7864). According to NIST the scoring is 21/25, Highly Critical.
A rating of anonymous access + remote code execution should result, according to risk management, in a patch immediately request!
Mitigation and Solution
There is only one workable solution to deal with this vulnerability: patch. Drupal also provides updates for non supported version.
- 8.5.x, upgrade to Drupal 8.5.1
- (no longer supported) 8.3.x, upgrade to Drupal 8.3.9
- (no longer supported) 8.4.x, upgrade to Drupal 8.4.6
- 7.x, upgrade to Drupal 7.58
- (no longer supported) 6.x, contact a D6LTS vendor
If you are unable to upgrade immediately then converting the Drupal site to a static HTML website might be a temporarily solution. This conversion can come at a cost (required resources and degraded features). One of the modules that can take care of this is Drupal Site Generator
Upgrading Drupal versions in a crisis situation is never a good idea but there are some guidelines that you can use Make an Upgrade Plan
.