VMware Workstation
I run a lab with a couple of Windows VMs on different laptops via VMware Workstation (for Linux). Some of these machines are “vulnerable” Windows systems (check out Microsoft Evaluation Center). I pretty much always use the same password for the administrator account to make management easy. This is bad practice for a real-life environment, but the purpose of these machines is to get compromised anyway.
However, sometimes it might seem like a good idea to change that password … and then you boot the machine after a couple of days of inactivity and can not remember the password.
Instead of rebuilding the machine from scratch I wanted to use a Windows recovery trick that I learned from one of my colleagues.
Recovering Windows Administrator Password
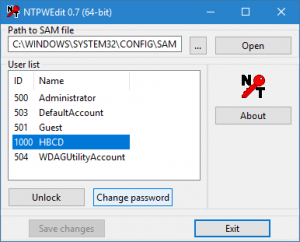
I remember the BartPE Windows environment on a LiveCD that allowed you to recover broken Windows installs. It turns out that there’s some sort of successor for this LiveCD, it’s now called : Hiren’s BootCD PE.
This LiveCD includes a feature to reset a Windows password, if you can boot the system from the USB. Resetting the password is pretty much point-‘n-click.
The pre-requisite is “boot the system from USB”. Back to the Windows VMs in VMware Workstation.
Adjusting VMware boot preference
The normal procedure to boot from the USB drive would have been : Connect the USB, Reboot the VM, hit “Escape”, select external drive from the boot menu. Unfortunately this doesn’t work. You have to tell your VM to boot from UEFI, the Unified Extensible Firmware Interface.
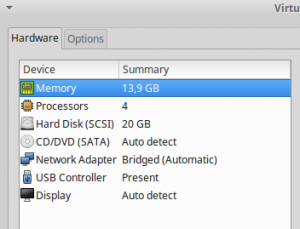
Changing this is pretty easy, at least on VMware Workstation for Linux. First go to the Settings screen.
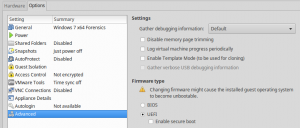
and then to the Options tab. Set the Firmware type to UEFI.
Then reboot the machine with the USB key plugged-in.
Once you have reset the password (see above), you have to set the firmware type back to BIOS.
This will probably seem pretty obvious for seasoned system administrators, but instead of having future Google-quests I decided to write this down for my own reference.

