Malware analysis, signatures and CERTs
CERTs have to provide their constituency early warnings and alerts about new threats.
A typical example is a new form of malware being distributed by e-mail. It takes a while before anti-virus vendors include the new signature to recognise the malware. This means that there’s a time window where the malware is not filtered and users in your constituency can get infected.
To protect your constituency you can provide them your own signature with indicators of compromise describing what the malware does exactly, how to detect it and possibly prevent it from weaponizing further. The process of getting these indicators from a binary is malware analysis.
Doing it manually can be time consuming, difficult and not always feasible. By the time you have finished your analysis there’s already a new mutated form of the malware.
Automated malware analysis
An automated analysis saves you time. You feed it the presumably malicious file and once the analysis is done you have a basic set of IOCs (Indicator of Compromise) that you can distribute to your constituency (possibly via a malware information sharing tool).
Automated analysis also allows you to analyse the behaviour of the malware in different configurations. Think of situation where you have to support multiple versions of Microsoft Office or Adobe Acrobat Reader.
There are several malware analysis sandboxes and services that can examine malware automatically but in this post I focus on one product : VMRay Analyzer.
VMRay
Some of the features of VMRay Analyzer are
- it covers different windows flavors;
- process creation, code injection, and driver installation methods are tracked and detected;
- analysis of contemporary 64-bit kernel rootkits;
- the client-server-architecture allows distribution of jobs.
VMRay got my attention because it claims to be impossible to evade, to be fast and to be reliable. Also I was searching for something similar to CWSandbox. The author of CWSandbox is the CEO of VMRay.
I requested and received a 30-day evaluation account to test the product.
VMRay technology
The first generation of malware analysis platforms used emulation. This delivers good results but can quickly become very slow. The second generation used hooks. This is faster but comes at a price. Hooks can be detected and can allow malware to prevent the analysis.
VMRay positions itself as the third generation of malware analysis because of its microprocessor functionality and monitoring methodology. Malware would be oblivious of it being monitored. Of course it would still be able to detect that it’s being run in a virtualization environment but, because of the high adoption of virtualization, that’s for most malware not an issue.
VMRay runs on commodity hardware and you can interface with it via a web browser.
VMRay evaluation
VMRay provides you a hosted test environment. In a production environment you can (or should) have the solution hosted in your premises. This limits the exposure that you give to “sensitive” malware. You still have the possibility to share your information with a community.
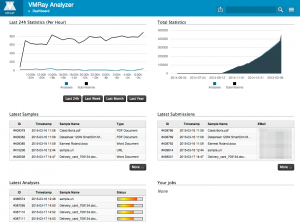
After logging in to the secured website you get the dashboard with an overview of your latest samples, analysis and submissions.
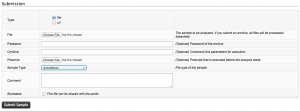
Submitting a sample is straightforward with one-click. You can provide a password (for archives) or extra command line options. A check box allows you to choose if you want to share the sample. Basically you just have to add the file and click submit to get it working. The sample type is automatically detected but you can also preset it to the different PE flavors, Word, Powerpoint, Excel, Flash, ….
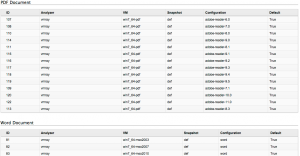
The analysis is done by a set of rules. The overview of these rules gives you an idea of what is supported in which specific configuration. These rules also allow you to better understand how the artifact behaves with different versions of the operating system or user applications.
Once the analysis is done you get a notification e-mail.
And then the juicy part begins.
VMRay evaluation – analysis
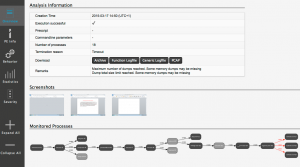
The submissions get analyzed simultaneously in different environments / configurations. This is great because it allows you to easily compare the behavior in different setups. When the analysis is finished you can either download the report (as a zip) or view it online.
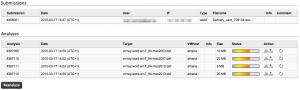
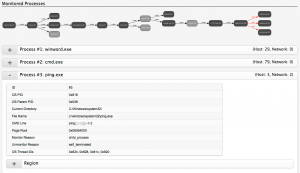
The Overview tab lists what has happened. It lists the time it took to complete, a process tree, screenshots and details of dropped or created files. The screenshots and the process tree are valuable to quickly see how the sample behaved in that specific environment. From here you can also download the entire PCAP or the logfiles. Having access to the PCAP file is fun because it gives you access to the bare-metal network details and you can do your own statistics (and network analysis).
The Behavior tab gives a detailed overview of what happened. The behavior is split out per process so you can exactly track the different stages of the sample.
Test sample : a Word document
One of my test samples was a Word document that is recognized by Virustotal as a Trojan Downloader. The file arrived as an attachment to an e-mail. My test case was to quickly extract the IOCs for detecting infected machines.
The submitted file got analyzed with four different Windows configurations (Office 2003, Office 2007, Office 2010 and Office 2013). I downloaded the report for the analysis done with Office 2010.
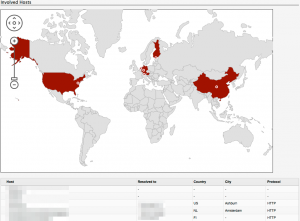
The overview tab showed that the malware does two ICMP requests to a host in China and creates a number of local files. With the outgoing ICMP traffic and the list of dropped files and their MD5 I can start the IOC signature. I have MD5 checksums that can be used for detection by a host IDS and I have network addresses that should be monitored for ICMP traffic.
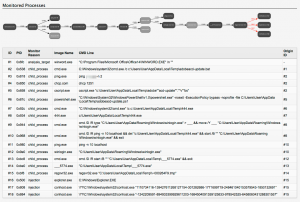
In the behavior tab I can see that next to the ICMP packets there are also a couple of HTTP requests. This allows me to extend the IOC signature with a list of network hosts to monitor.
With the help of the automated analysis of this sample I was able to quickly extract useful IOC data. The process did not involve a lot of work, merely uploading the file, waiting for the notification e-mail and reading the report.
VMRay API
VMRay can be used via the web interface or via an API. The API allows you to submit new samples and download the reports. This allows further integration within your existing environment and extensive automation.
Think of a situation where you isolate a new piece of malware and submit it for analysis. Once the job is done you can extract the relevant IOCs (network information, file hashes) and push these to your threat intelligence for sharing and to your security solutions for further monitoring.
Conclusion
I love the ease of use and the flexibility of VMRay. It’s a great addition to the toolset of a CERT, without a lot of manual intervention. This is important because you do not want to spend your resources on babysitting your own lab for every analysis.
The access to the PCAP and log files allows you to analyse the network stream and build your own statistics.
Some of the samples were already manually analysed so I knew what to expect. As far as I could tell none of the automated analysis missed a pointer.
The support during the evaluation period was good. I got quick and detailed replies on my questions.
It is not immediately possible to extract IOCs. But the log files (in XML format) resulting from the analysis allow you to extract the necessary information with your own scripts. Future versions might include XML logfiles that include the high level details, this would make IOC extraction even much easier.
VMRay is currently focused on Windows environments but other platforms (ARM, OSX) might be integrated in the future.
VMRay gets its biggest strength from a lot of simultaneous analysis of malware running in a predefined set of configurations.
During my tests I did not encounter any functional issues. The few remarks that I had were quickly dealt with or I got a satisfying explanation. I’ve not been able to test it with complex malware families but as far as I could check it did its analysis job flawlessly.


hmm i would love to use your tool for the project im currently working on. I’m doing a research on malware analysis and honestly while I’m interested in the topic I find it a bit abstract cause I’m finding it hard writing the methodology for my paper. I feel automation would be a good idea for my analysis. Any idea as to how to go about it?
Please contact https://www.vmray.com/contact/ for information on usage licenses for VMray.