ICS
Industrial Control Systems or ICS have received a lot of attention lately. In the US the ICS-CERT was established and ENISA has a whole unit devoted to Industrial Control Systems/SCADA. But for most people working in IT it is still a relatively new playing field.
Because every area in technology has its own specific vocabulary I wrote a small intro to PLCs, ICS and SCADA of the different components that play in the ICS field.
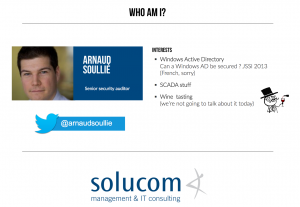
This summary is based on a video of a workshop Industrial Control Systems : Pentesting PLCs 101 at Black Hat. The workshop was given by Arnaud Soullié. The video contains much more details than covered in this post so be sure to check it out. The downside of video material is that it isn’t that easily accessible as a reference … hence this post.
What is PLC, ICS, SCADA?
What is an ICS?
What is an Industrial Control Systems or ICS? An ICS is divided into different parts.
- Production network
- Sensors, the input and output to the PLCs
- RTU, the Remote Terminal Units (a PLC, to be used remotely)
- Contains classical wireless networks
- Supervision network
- Sometimes called the SCADA network
- Workstations with the supervision software installed
- This is the place from where engineers manage the processes
- Maintenance laptops
- Servers specific to the process
- Corporate network
- Workstations
- Connected with supervision network for gathering data for optimization
- Import data to SAP (or any other ERP)
What we call ICS is basically production and supervision network. It is the network that has the connection with the physical world.
Vocabulary
A bit of vocabulary:
- ICS : Industrial Control System
- IACS : Industrial Automation and Control Systems
- SCADA : Supervisory Control And Data Acquisition
- DCS : Distributed Control System
Remember that SCADA is only one part of the ICS but sometimes people mix the terms. If someone refers to SCADA make sure that they don’t mean the entire ICS.
ICS Components
An ICS often consists of these components
- Sensors and actuators : The connectors to the real physical world. Consider the sensor as some kind of switch and the actuator as the component that does the action.
- Local HMI : Human Machine Interface, useful to interact with a subprocess
- PLC : programmable logic control manages the sensors and actuators
- Supervision screen : remote supervision of the industrial process
- Data historian : records data and allows exporting to the corporate network
Stuxnet: game changer
The discovery of Stuxnet in 2010 / 2011 changed the view on ICS security. What is currently wrong with ICS security?
- No awareness : they care about physical safety and not security, often remote access of the process is not always assessed properly;
- Limited staff : only a few people involved with IT (and that most often does not mean ‘security’);
- Lack of network segmentation : There are no real DMZ or firewalls. The access control is done via ACLs on routers. Sometimes it’s fairly easy to jump from the corporate network to the ICS network;
- Vulnerability management : it is not easy to apply patches because you can not just shut down a plant. Often the Windows machines are not patched (sometimes because they are not connected to the Windows Update Systems). PLCs are sometimes updated with firmware updates but patching also requires a shutdown of the industrial process. Because of this, although the patches are published they are rarely applied;
- Security protocols : there is no IT security included in the protocols (no authentication, clear text protocols, …);
- Third party management : some environments need to allow remote support to their specific devices;
- Security supervision : ICS is all about monitoring a process, not monitoring the security state of a process.
ICS is about monitoring an industrial system, not monitoring the security state of a system.
What is a PLC?
A PLC is a programmable logic control. It is some kind of real-time computer. It is designed to manage input and output of processes. It was invented to replace electric relays.
It consists of hardware, firmware/OS and applications. The last is one is the programmable logic that is run through the middleware. There are different ways to program a PLC. The “ladder logic” was the first programming language for PLC, as it mimics the real-life circuits. Afterwards there were 5 programming languages defined for PLCs.
Unity Pro is software that you have to use if you want to control most of the Schneider PLCs.
Where do you find systems on the Internet?
You can find a list of systems (not restricted to PLCs) connected to the Internet via Shodan. You can search for “interesting” strings. For example search for Schneider PLC: M340 or S7-1200.
Modbus
Modbus Protocol
Modbus is a serial communication protocol. It is the most widespread used protocol within ICS.
I have a separate blog post with an introduction to Modbus TCP traffic.
Detecting PLCs
Next to using Shodan you can use a couple of scripts to detect PLCs on your network. A word of warning. The TCP/IP stack in some PLCs might not be fully mature. If you send uncommon traffic you might crash the PLC. Never do the scanning without permission.
You can use
- nmap : network port scanner
- PLCScan : PLC devices scanner (port 102 for Siemens, port 502 for Modbus)
Nmap has a script to query for example Modbus devices and Siemans S7 PLC devices.
sudo nmap -p 502 -sV --script modbus-discover 127.0.0.1 sudo nmap -p 102 -sV --script s7-info 127.0.0.1
Detect attacks on ICS devices
There are a number of techniques and tools that you can use to detect attacks on ICS devices. A large number of these attacks will contain a network component. This means that using basic network security monitoring and intrusion detection will already get you very far.
Honeypot
Conpot is a low interactive server side Industrial Control Systems honeypot designed to be easy to deploy, modify and extend.
Industrial Control Systems Library: Poster
The Fall 2015 poster from the SANS institute details the SANS ICS Curriculum and what categories of actions contribute to security.
Introduction to Modbus TCP traffic
I have a separate blog posting with an introduction to Modbus TCP traffic


This is great information. I work in a food manufacturing plant and this would be ideal for us. We are a smaller facility, but I think we could benefit from this kind of monitoring technology. We have a long 200′ oven with equipment on both ends. Having a place where we can see what is happening on both ends would be so much more efficient.